Topic: identity
Will Kubernetes Become the Standard for AI Workloads?
The answer, of course, is that it depends. But the Cloud Native Computing Foundation (CNCF) announced some major steps forward toward this goal at the KubeCom Europe conference last week in Amsterdam. This was the biggest KubeCon ever with about 13,500 attendees, representing an 8% growth over last year, reflecting CNCF’s extraordinary success in establishing … continue reading
Credential Management: The Hidden Production Bottleneck for Agentic AI on Kubernetes
Agentic AI has moved from experimental curiosity to a production imperative. Organizations are deploying AI agents that don’t just answer questions but take actions: querying databases, updating records, orchestrating workflows, and provisioning infrastructure. These systems are no longer confined to innovation labs and are increasingly embedded in core business operations. The question is no longer … continue reading
Reducing engineer burnout through unified identity
Not long ago, engineering teams mainly focused on building and running systems. That was the job. But if you look at the average engineer’s job role today, it’s a very different picture. The average tech stack has expanded massively, to include multiple clouds, clusters, databases, and environments, not to mention a growing number of tools, … continue reading
SailPoint Accelerated Application Management facilitates application governance at scale
SailPoint, an enterprise identity security company, is introducing a new solution to help organizations discover, govern, and secure their growing number of applications. SailPoint Accelerated Application Management provides continuous application discovery to uncover inventory, ownership, user activities, and risky access patterns. According to the company, this visibility enables IT teams to identify high-risk applications, prioritize … continue reading
1Password adds new capability to enable AI agents to securely access and manage secrets
1Password announced new and upcoming updates to its Extended Access Management platform. Announced last year, Extended Access Management promises to “secure every sign-in, for every app, on every device.” Available today, the company announced a new SDK for Agentic AI within the platform to allow developers to enable the AI agents they build to securely … continue reading
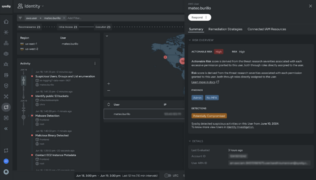
Sysdig Cloud Identity Insights automatically detects compromised user accounts
Sysdig has launched a new solution, Cloud Identity Insights, that will make it easier for companies to detect compromised identities so they can act faster to contain problems. The company explained that according to a report from Verizon, almost 40% of data breaches are the result of compromised accounts. Therefore, suspicious user activity is often … continue reading